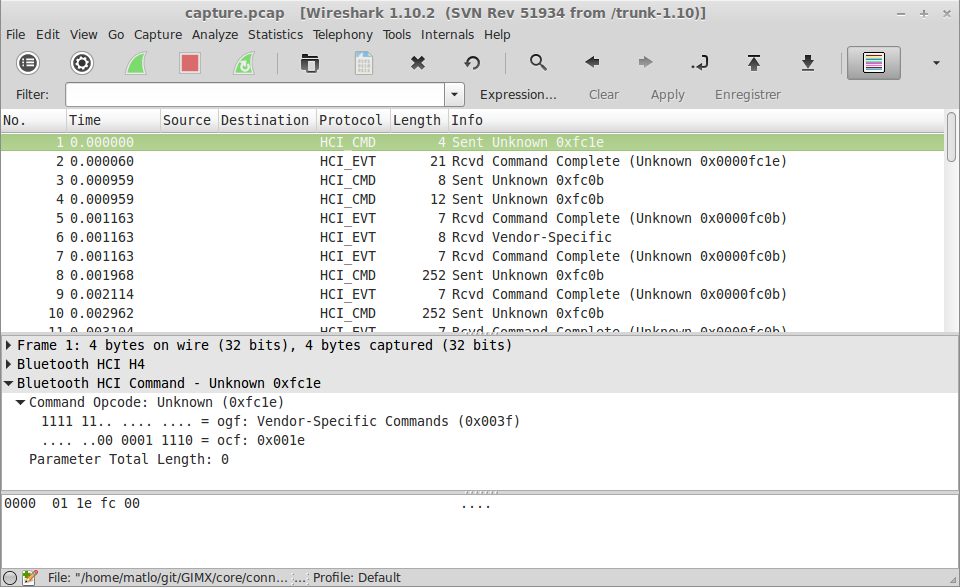
My current task consists in reverse engineering the Bluetooth HID protocol used by the PS4 and the DS4. I’m sharing the result of this work on the DS4 page of Frank’s wiki. This is not a trivial task but I made it easier since I have a L2CAP proxy that allows man-in-the-middle operations, like skipping specific transfers or modifying specific bytes within specific transfers.
The most difficult transfers to understand are those that are carried over the HID control channel (SET and FEATURE reports). The transfers that are carried over the HID interrupt channel are easier to understand: input reports carry axes and buttons states from the DS4 to the PS4, and output reports carry rumble, led and audio data from the PS4 to the PS4.
This work will eventually allow to cleanly implement the DS4 protocol in GIMX.