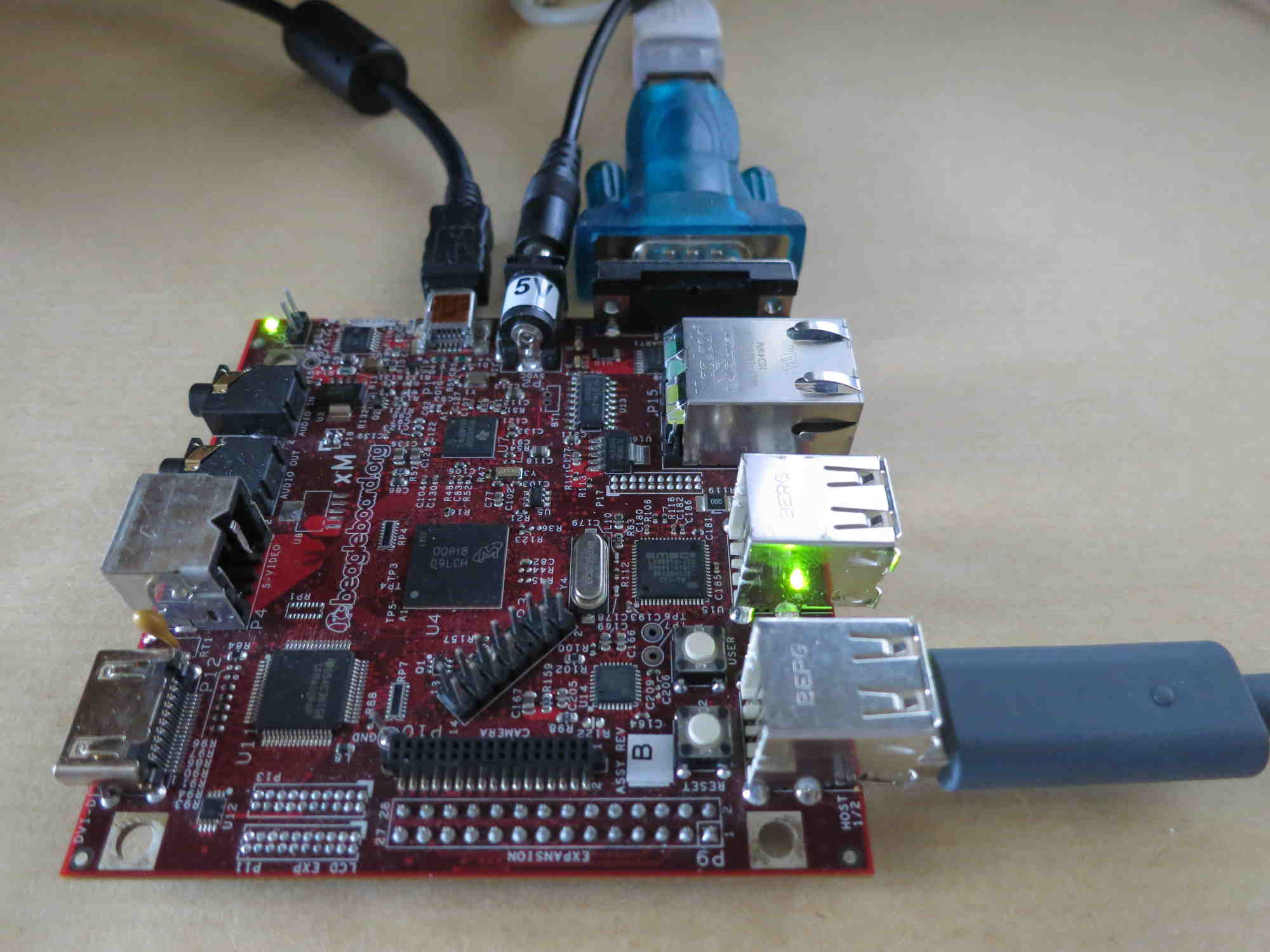
In recent weeks, I have been working on serialusb, a cheap USB proxy for input devices.
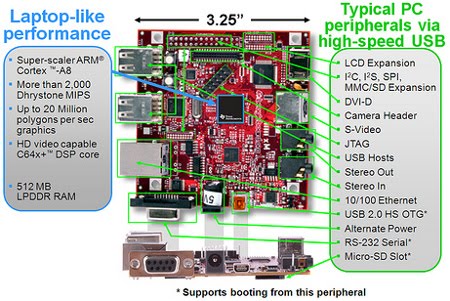
This tool can act as a USB proxy using the well-known DIY USB adapter.
Combined with usbmon and wireshark, it allows to generate and inspect USB captures.
Read the github project page to learn about the capabilities, the limitations, and the usage instructions of serialusb.
I’ve tested it successfully with the following hosts and devices:
- PC + Logitech G502 gaming mouse
- PC + Dell USB keyboard
- PC + Logitech Driving Force GT
- PC + Logitech RumblePad 2
- PS3 + Logitech Driving Force GT
- PC or PS3 + Dualshock 3
- PC or PS4 + Hori Pad Fps plus
- PC or Xbox 360 + Xbox 360 controller
- PC or Xbox One + Xbox One controller
If you have a DIY USB adapter and any of the following host + device combination, please consider making a USB capture and send it to me:
- Xbox One + Logitech G920
- Xbox One + Xbox One controller with 3.5mm stereo headset jack (USB PID = 0x02dd)